This is a continued post from Part 1, which can be found HERE.
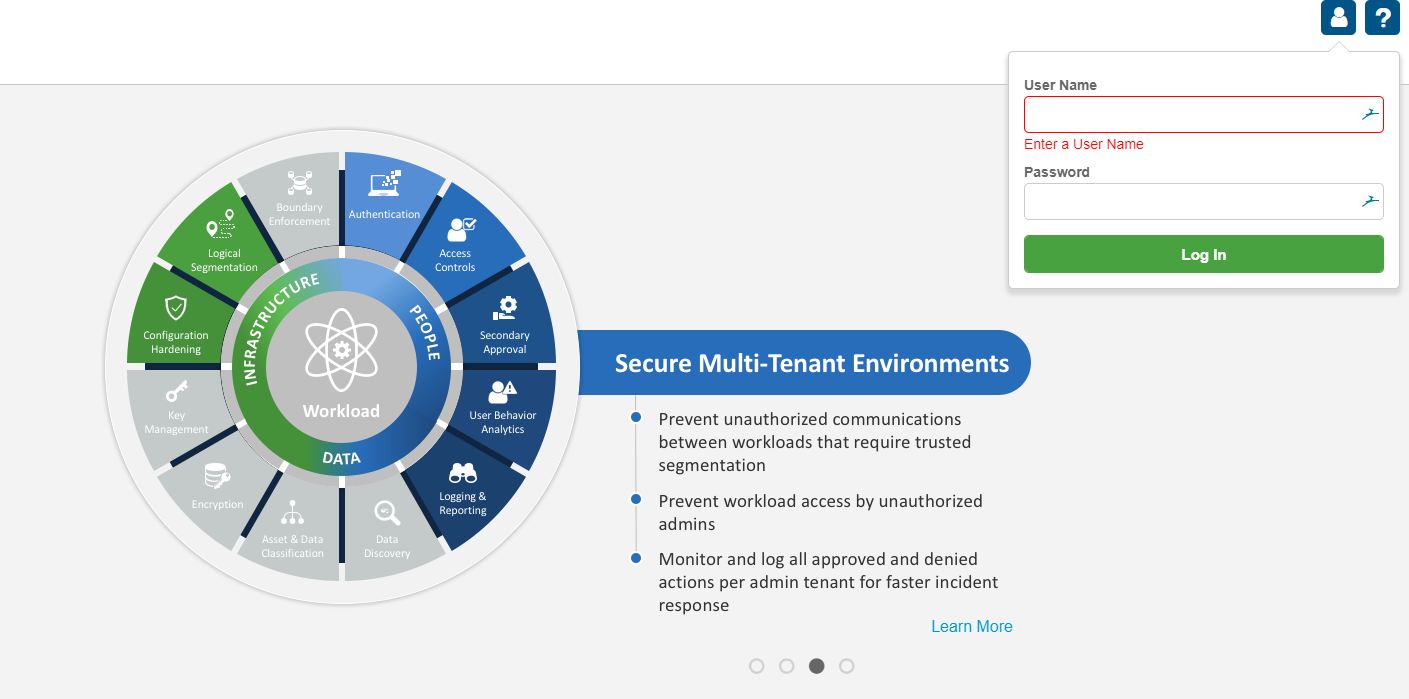
Step 4: Browse to the IP address (or hostname if DNS is setup) in Step 3 and enter the credentials.
Creds: Username: secroot Password: secroot
Agree to the EULA – only if you agree! 😉
Change the Password for the secroot account. Be sure to make it something secure.
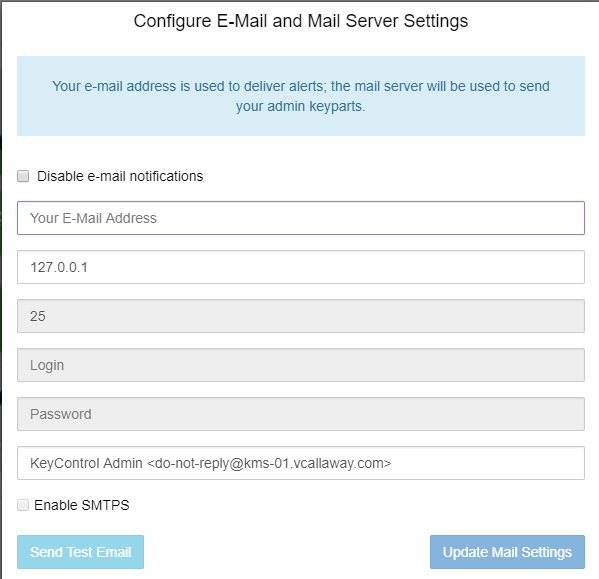
Once complete with that, enter in any SMTP settings, if desired.
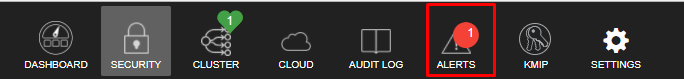
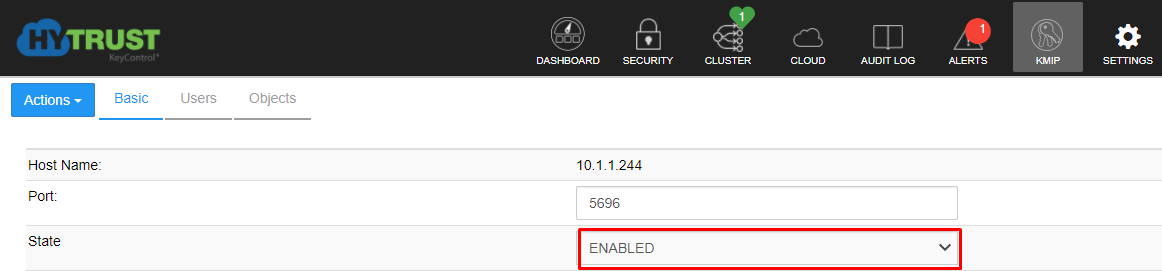
Now that we’re complete with that, it’s time to configure KMIP.
Step 5: Configure KMIP
Very Important! To Enable KMIP we need to change the STATE from disabled to enabled, click Apply, Proceed.
Keep in mind the port number, we’ll need it later in step 9.
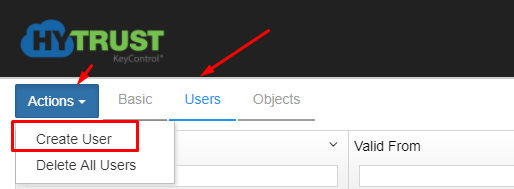
Step 6: Create a User
Click on Users tab, under Actions, click on Create.
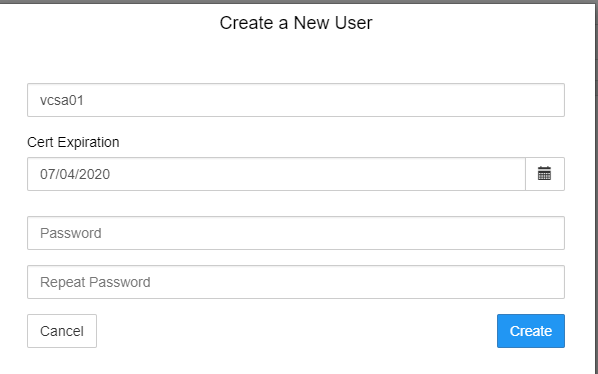
Step 7: Name the user. Doesn’t matter the name. Most likely something easy to reference.
**Important Note – Do NOT set a password here. It will cause an issue during setup.
Step 8: Highlight the newly created user, click Actions, Download Certificate. Download the .zip file to somewhere easy to retrieve, we will need it shortly.
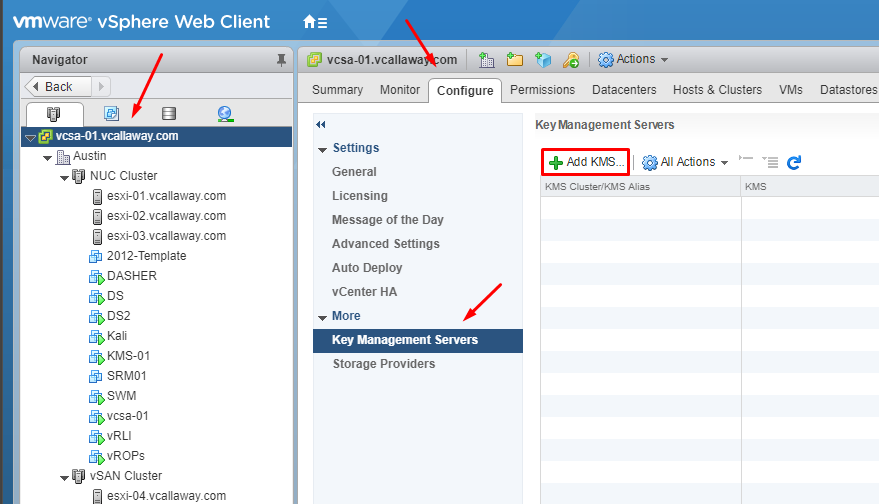
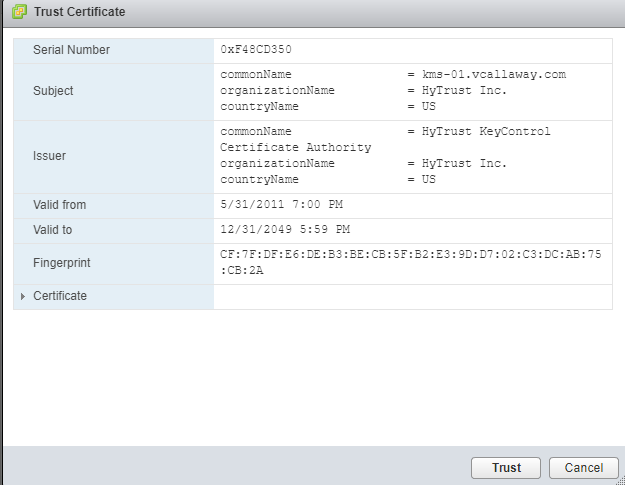
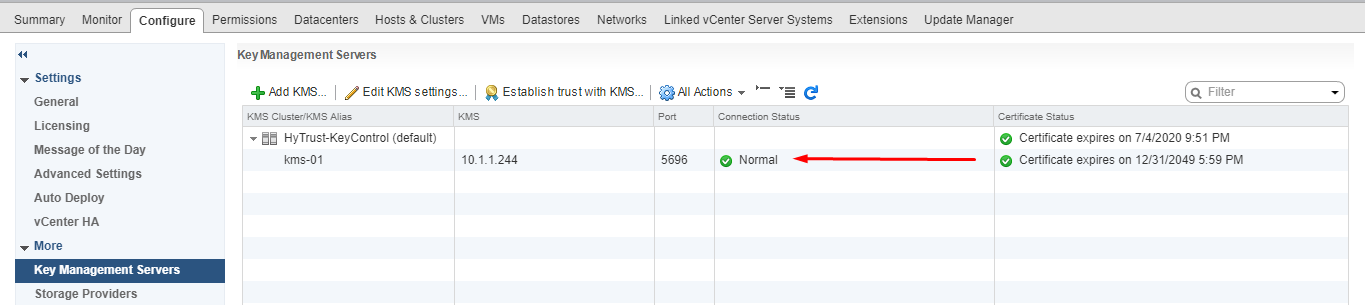
Step 9: Head back to the VCSA Web Client and navigate to the top level vCenter, Configure tab, and then Key Management Servers
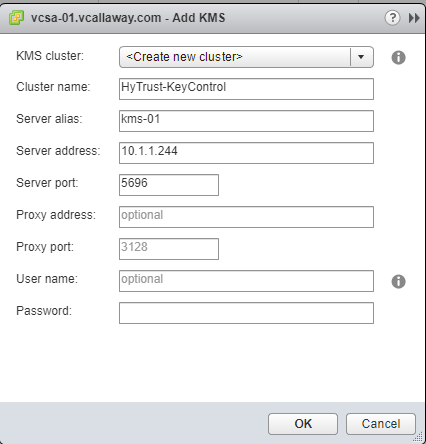
Enter a Cluster Name, Server Alias, Fully Qualified Domain Name (FQDN) and the port number. (Port number is 5696 from Step 5)
**Important Note: Leave username and password fields blank
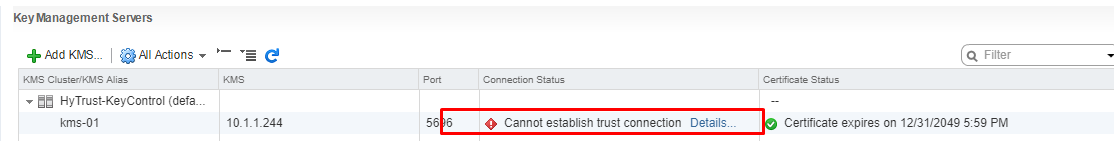
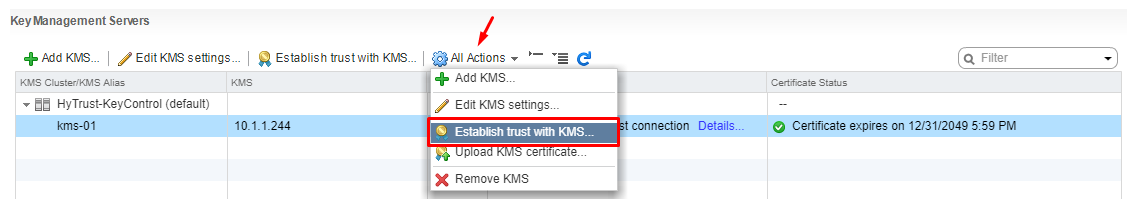
We’re not done yet. We need to establish a trust relationship between vCenter/VCSA and HyTrust KeyControl.
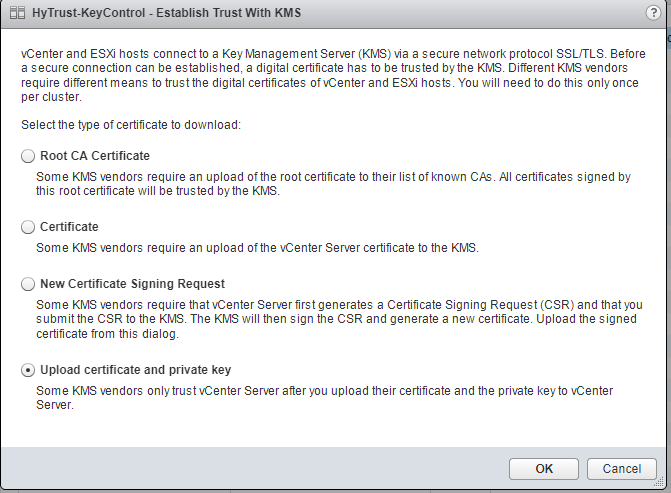
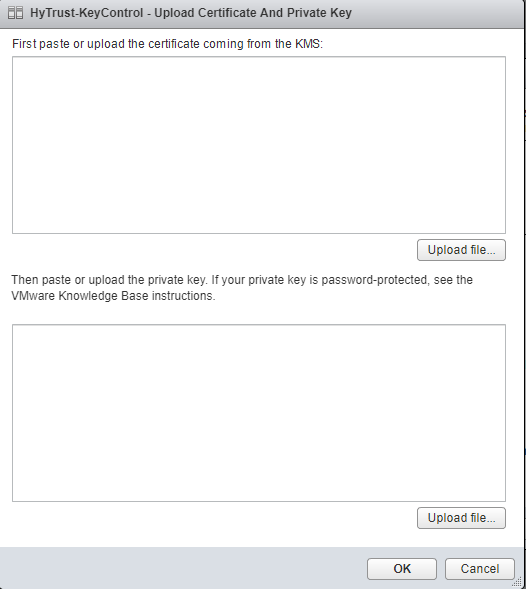
Select Upload Certificate and Private Key
Click OK
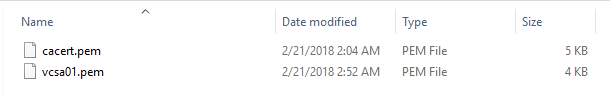
We need to enter the certificate keys we exported earlier. Navigate to the saved location and unzip the file. You should see 2 files.
Open the vCenter file (in this case it’s named vcsa01.pem). Paste this into the Certificate box. Do the same for the private key. Alternatively you can just upload the file as well.
Next post will cover how to encrypt a VM. Stay tuned!


Hey,
When you set up hytrust. Are you able to make rest calls to the vCenter (like using postman or something). I am having trouble and i am not able to create a rest session using the hytrust url